Understanding Data Erasure: Why It Matters
The need for strong data sanitisation goes beyond simple security upkeep; it is a core requirement for legal compliance and protecting your brand.
The Growing Threat of Data Breaches
Data breaches continue to affect organisations across all sectors. When sensitive assets—like customer records, intellectual property, or financial data—are compromised due to poor disposal, the consequences can be severe.
Compliance with Data Privacy Regulations (GDPR)
The General Data Protection Regulation (GDPR) requires organisations to use appropriate security measures to protect personal data, which clearly includes secure data disposal. Failing to meet these requirements can lead to significant financial penalties.
Protecting Your Reputation and Brand Image
A data leak caused by retiring devices insecurely can instantly damage customer trust and cause lasting harm to an organisation’s reputation. Taking proactive, verifiable steps toward data erasure shows a real commitment to security.
Legal and Ethical Considerations
Organisations have both a legal duty and an ethical obligation to protect the data entrusted to them. Following recognised standards proves that due diligence was performed when retiring assets.
Key Data Erasure Terminology
Data sanitisation is a wide term covering several techniques, each suitable for different security needs.
- Data Sanitisation
- This general term includes all methods used to make data inaccessible, grouped by the required security level.
- Clearing
- This involves overwriting data with non-sensitive information, like zeros. It works for data that doesn’t need the highest security clearance.
- Purging
- Purging aims to make data unrecoverable even using advanced lab techniques. This usually means multiple, patterned overwrites or cryptographic erasure.
- Destruction
- This is the most final method, involving physically destroying the storage device itself (e.g., shredding or crushing), ensuring the data cannot be recovered at all.
- Overwriting
- The process of replacing existing data on a storage medium with new data, often using random characters or a fixed pattern.
- Degaussing
- Using a powerful magnetic field to scramble the magnetic domains on traditional hard drives (HDDs) and tapes, effectively erasing the stored data. This method does not work on solid-state drives (SSDs).
- Cryptographic Erasure
- This method involves securely destroying the encryption key used to protect the data. If the key is gone, the encrypted data becomes permanently unreadable.
NIST 800-88: Guidelines for Media Sanitization
Developed by the National Institute of Standards and Technology (NIST), NIST 800-88 Revision 1 is the widely accepted benchmark for sanitising data across various media types, including HDDs, SSDs, tapes, and mobile devices. It offers a clear structure based on data sensitivity and the risk of recovery.
NIST 800-88 Sanitisation Levels
NIST defines three main levels of sanitisation:
Clear
This level is suitable for data that is not considered highly sensitive.
- Recommended Methods: A single-pass overwrite using zeros or random characters is often enough for media that will stay within the organisation’s control.
Purge
This level is necessary for data that requires a higher security posture.
- Recommended Methods: This involves multiple overwrites using different patterns, degaussing (for magnetic media only), or cryptographic erasure.
Destroy
This level is required for media holding highly sensitive data or when the storage device is otherwise unusable.
- Recommended Methods: Physical destruction, such as shredding, crushing, or incineration, ensuring the media platters or chips are rendered inoperable.
Applying NIST 800-88 to Different Storage Media
NIST 800-88 recognises that modern storage setups need tailored approaches. For example, standard overwriting methods often fail for SSDs because wear-levelling algorithms spread data across many physical blocks, making a single overwrite pattern unreliable.
DoD 5220.22-M: The Department of Defense Standard
The DoD 5220.22-M standard, which was historically part of the National Industrial Security Program Operating Manual (NISPOM), set out procedures for sanitising storage media used by US government contractors.
The DoD 5220.22-M Overwriting Process
This standard is best known for its requirement of multiple overwrite passes, often described as a 7-pass process. This usually involved writing a specific pattern, its opposite, and then a random pattern, repeated seven times, followed by a final verification pass.
Limitations of DoD 5220.22-M
While historically important, the DoD standard is increasingly seen as outdated, especially concerning modern storage technologies. Its reliance on sequential overwriting does not account for the complex internal mapping used by SSDs, making it less reliable for solid-state media than NIST guidelines. In many current situations, NIST 800-88 has replaced DoD 5220.22-M as the preferred best practice.
NIST 800-88 vs. DoD 5220.22-M: A Detailed Comparison
Knowing the differences between these two major standards is key to choosing the right disposal strategy.
Key Similarities
Both standards aim to stop data recovery through software by requiring data overwriting as a main sanitisation technique. Both also require some form of verification to confirm the process succeeded.
Key Differences
| Feature |
NIST 800-88 (Rev. 1) |
DoD 5220.22-M |
| Scope |
Broad guidelines for all media types (HDD, SSD, Tape, Mobile). |
Primarily focused on magnetic media (HDDs/Tapes). |
| Methodology |
Groups methods into Clear, Purge, Destroy based on risk. |
Specifies exact, multi-pass overwrite sequences (e.g., 7-pass). |
| SSD Suitability |
Directly addresses SSD issues, recommending Secure Erase or Cryptographic Erase for purging. |
Ineffective for SSDs due to wear-levelling issues. |
| Current Relevance |
Considered the current global best practice. |
Mostly historical; often referenced but superseded by NIST for modern compliance. |
Which Standard Should You Choose?
For most commercial and regulatory compliance needs in the UK, NIST 800-88 offers the most current, flexible, and technically sound framework. It lets organisations match their erasure method exactly to the sensitivity of the data being destroyed, rather than sticking to a rigid, potentially ineffective, multi-pass routine.
Choosing the Right Data Erasure Method
Picking the right method depends on several important factors related to the hardware and the data it contained.
Factors to Consider
When deciding on the best approach, evaluate:
- Data Sensitivity: Was the data highly confidential (requiring Purge/Destroy) or general business information (suitable for Clear)?
- Storage Media Type: HDDs handle degaussing and overwriting well; SSDs need specific commands like Secure Erase or physical destruction.
- Regulatory Requirements: Does your industry require adherence to a specific standard (e.g., financial services or healthcare)?
- Budget and Time: Physical destruction is fast but expensive; software erasure is cheaper but takes longer.
Data Erasure Software
Modern erasure software tools are built to automate the NIST-compliant process, often incorporating device-specific commands (like ATA Secure Erase for SSDs) and providing detailed audit reports.
Data Erasure as a Service (DEaaS)
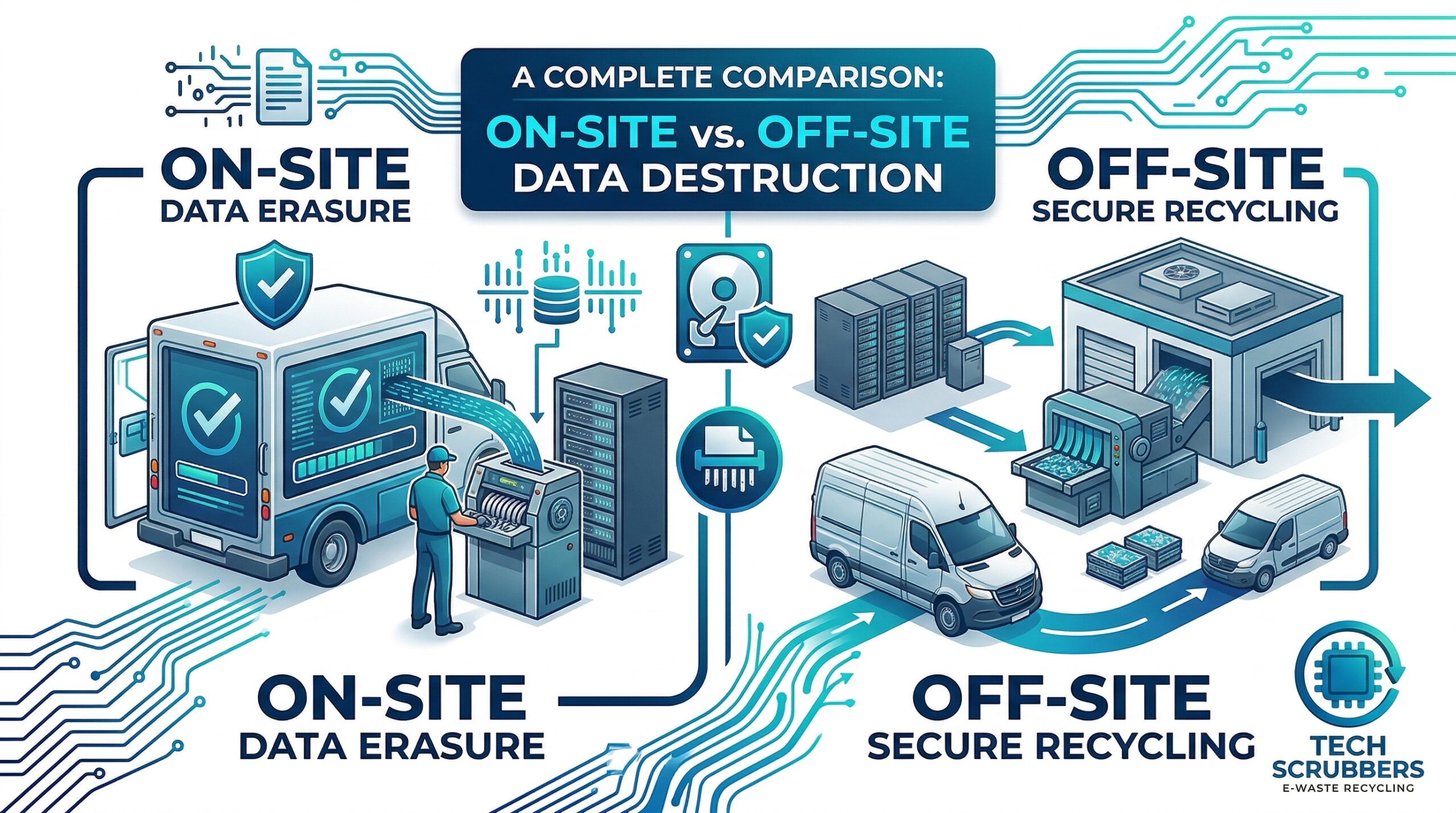
Hiring specialised providers like TechScrubbers for data erasure offers major benefits. Professionals bring experience in handling different media, guarantee adherence to the latest standards, and supply verifiable certificates, taking the compliance management load off your internal IT staff.
DIY vs. Professional Data Erasure
While in-house erasure is possible, using professional services reduces the chance of human error, ensures the correct tools are used for every media type, and provides the necessary documentation required for audits.
Data Erasure Verification and Certification
The process isn’t finished until success is proven. Unverified erasure leaves an organisation open to liability.
The Importance of Verification
Verification confirms that the sanitisation process successfully overwrote or destroyed the targeted data sectors. Without verification, the erasure process is just guesswork.
Data Erasure Certification
A formal Certificate of Erasure creates a permanent audit trail. This document lists the media serial numbers, the standard applied (e.g., NIST 800-88 Purge), the date, and the technician in charge. This is vital evidence during regulatory audits.
TechScrubbers’ Data Erasure Process and Certification
At TechScrubbers, we strictly follow NIST 800-88 guidelines. Our process includes pre-scanning, applying the required sanitisation method (software or physical), post-verification scanning, and issuing a complete Certificate of Erasure for every asset processed, ensuring full compliance for our clients.
Data Erasure and GDPR Compliance in the UK
For companies operating under UK GDPR, secure data disposal is a direct compliance duty.
GDPR Requirements for Data Disposal
GDPR demands that personal data, once it is no longer needed for the original purpose, must be securely deleted or anonymised. This rule applies equally to data stored on retired hardware.
The “Right to be Forgotten”
Data erasure is the practical way organisations meet requests under the “Right to be Forgotten” (Article 17 of GDPR), ensuring personal data is permanently removed from all accessible storage.
Data Erasure as a Key Component of GDPR Compliance
Putting in place a documented, standards-based erasure policy is a fundamental part of any strong GDPR compliance strategy, showing accountability and appropriate technical safeguards.
TechScrubbers: Your Trusted Data Erasure Partner in the UK
TechScrubbers offers expert, compliant data sanitisation services tailored specifically for the regulatory environment of the United Kingdom.
Our Data Erasure Services
We provide complete data security solutions, specialising in applying NIST 800-88 standards across diverse IT estates, from single workstations to large data centre decommissioning projects. Learn more about our certified data erasure services.
Our Data Erasure Process
Our method ensures maximum security: we identify, catalogue, apply the correct NIST-level sanitisation (Clear, Purge, or Destroy), verify the results using top industry tools, and provide full documentation. We are skilled at handling the challenges of modern media, including SSDs and virtual environments.
Our Certifications and Compliance
We maintain strict internal standards that match UK data protection needs, ensuring every erasure project can be audited and fully complies with data protection legislation.
Serving Businesses in Manchester and Across the UK
Though based locally, TechScrubbers supports businesses throughout the UK, delivering reliable, secure, and certified data erasure solutions wherever your assets are located. Explore our secure on-site options.
Contact TechScrubbers today for a free consultation on achieving NIST 800-88 compliant data erasure for your organisation.
Request A Compliance Quote