On-Site vs. Off-Site Data Destruction: A Guide for UK Businesses
Ensure your organisation remains secure and compliant with professional on-site data erasure.
Book Your On-Site ServiceWith data privacy regulations becoming increasingly strict, secure IT asset disposal is no longer a back-office task; it is a core business requirement. Whether you are upgrading servers, replacing laptops, or decommissioning mobile devices, your chosen method for data sanitisation directly affects your risk profile. For many organisations, on-site data erasure has become the preferred method for maintaining total control over sensitive information.
Why Data Destruction Matters
Data destruction is the process of making information on storage devices unrecoverable. It is a fundamental part of IT Asset Disposition (ITAD). Under the UK General Data Protection Regulation (UK GDPR) and the Data Protection Act 2018, organisations are legally responsible for protecting personal data throughout its entire lifecycle, including the point of disposal.
On-Site Data Destruction: Maintaining Control
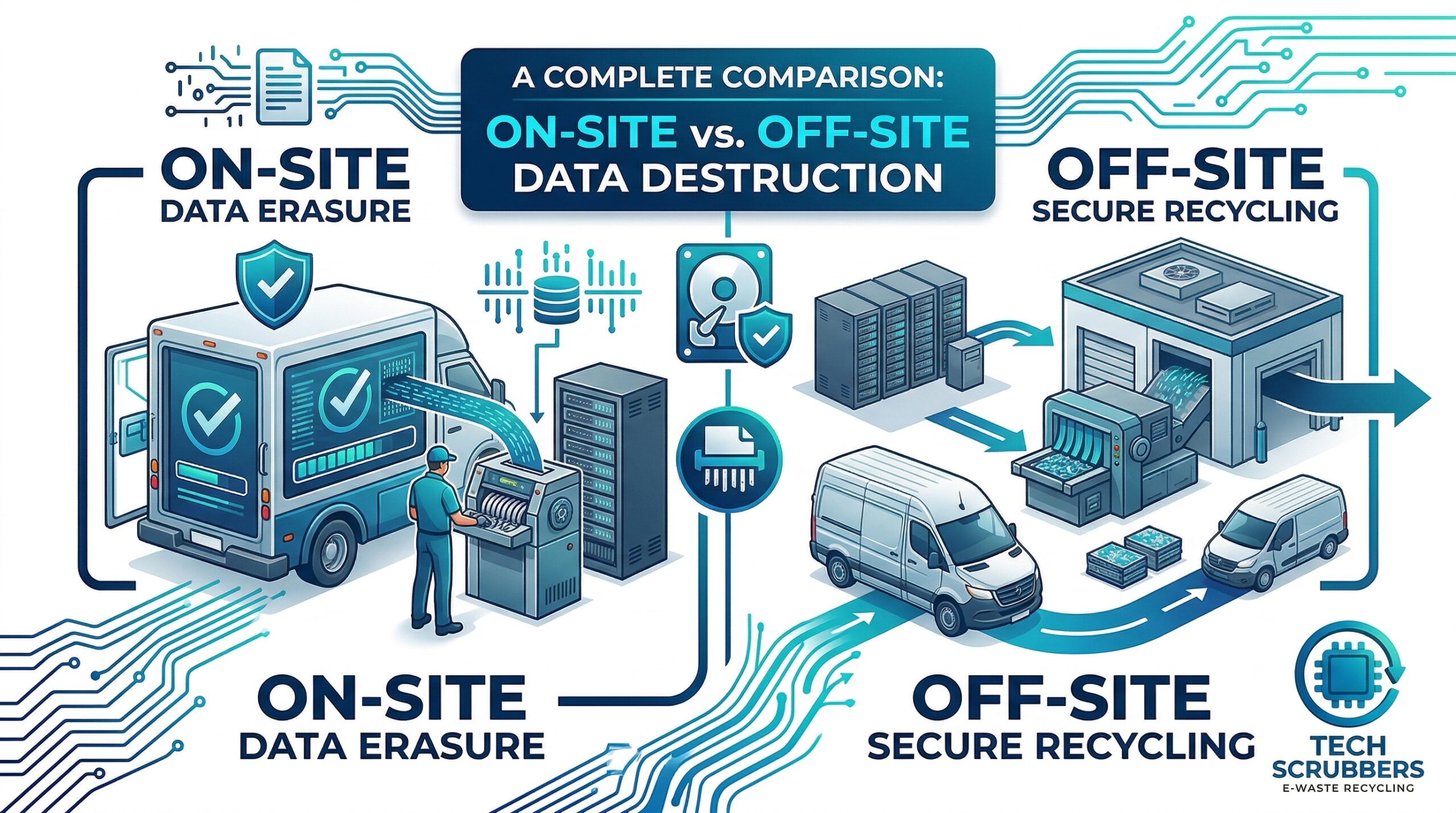
On-site destruction involves performing the sanitisation process at your own premises. This removes the risks associated with transporting sensitive hardware to a third-party facility.
On-Site Data Erasure (Software-Based)
On-site data erasure uses specialised software to overwrite every sector of a storage device with non-sensitive data. When done correctly, this makes the original information unrecoverable, even with forensic tools. Reputable providers follow international standards like NIST 800-88, ensuring the process is verifiable and audit-ready.
On-Site Physical Destruction
For faulty or redundant devices, physical destruction—such as industrial shredding, crushing, or degaussing—is the most definitive method. By shredding hard drives into fragments on-site, you ensure the media is destroyed before it leaves your sight.
Off-Site Data Destruction: Outsourcing Security
Off-site destruction involves a vendor collecting your IT assets and transporting them to a secure facility. While often marketed as a convenient solution, it introduces variables that businesses should carefully consider.
On-Site vs. Off-Site: Comparison
| Feature | On-Site Destruction | Off-Site Destruction |
|---|---|---|
| Security | High: Data stays on-site. | Moderate: Risk during transit. |
| Chain of Custody | Direct and transparent. | Dependent on third-party logistics. |
Techscrubbers: Your Partner for On-Site Data Erasure
At Techscrubbers, we specialise in secure, on-site data erasure for UK businesses. We know your data is a critical asset, and our goal is to ensure it remains protected until the moment it is erased. By bringing our certified processes directly to your facility, we provide the security and compliance that modern organisations need.
View Our Certification Process Read Our Full Guide